Dead-Drop service
So, for a while I've been hosting an instance of BillKeenan/dead-drop-python on one of my servers (by wrapping all that in a docker container). However, that was from a time, where I did not automate those deployed things, and when I tried to move this service to a new server, I was not able to build the dockerfile anymore (some kind of python dependency deprecation). That was the point, I finally decided to write such a service on my own (which I had in my head already for a longer time, but never took the initiative to).
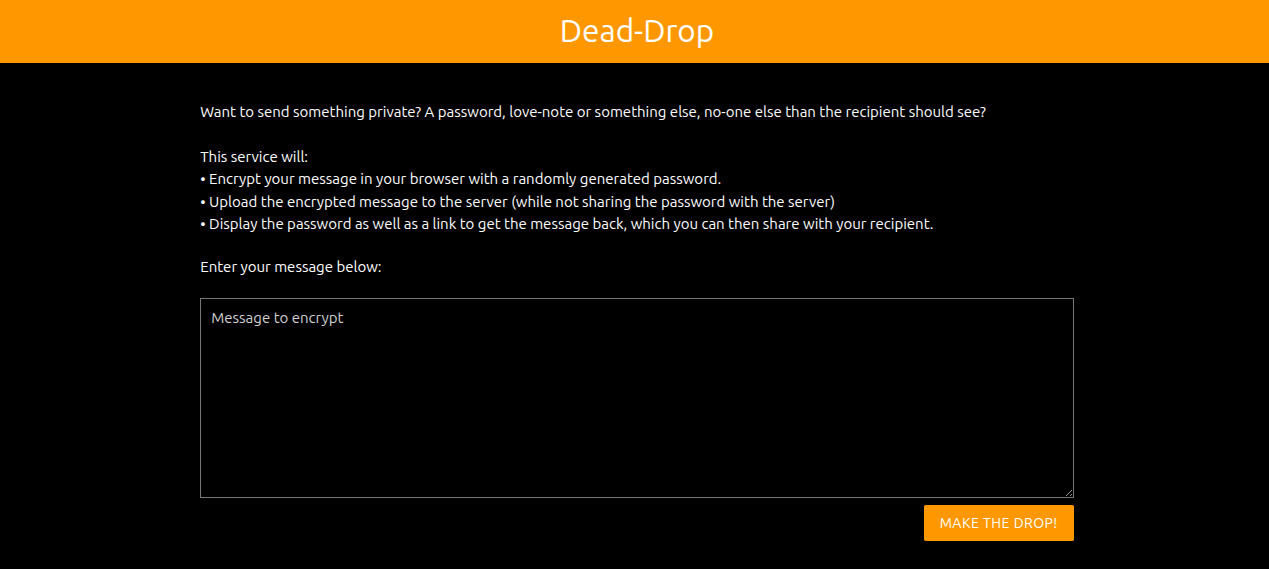
So, I've created a new, open source Dead-Drop service, written in Kotlin with KTor on the backend, and plain JS as well as sjcl on the frontend. The source-code is available at GitHub (as well as my self-hosted Gitlab), where the code can be inspected, as well as instructions to set this up on your own server using docker are available.
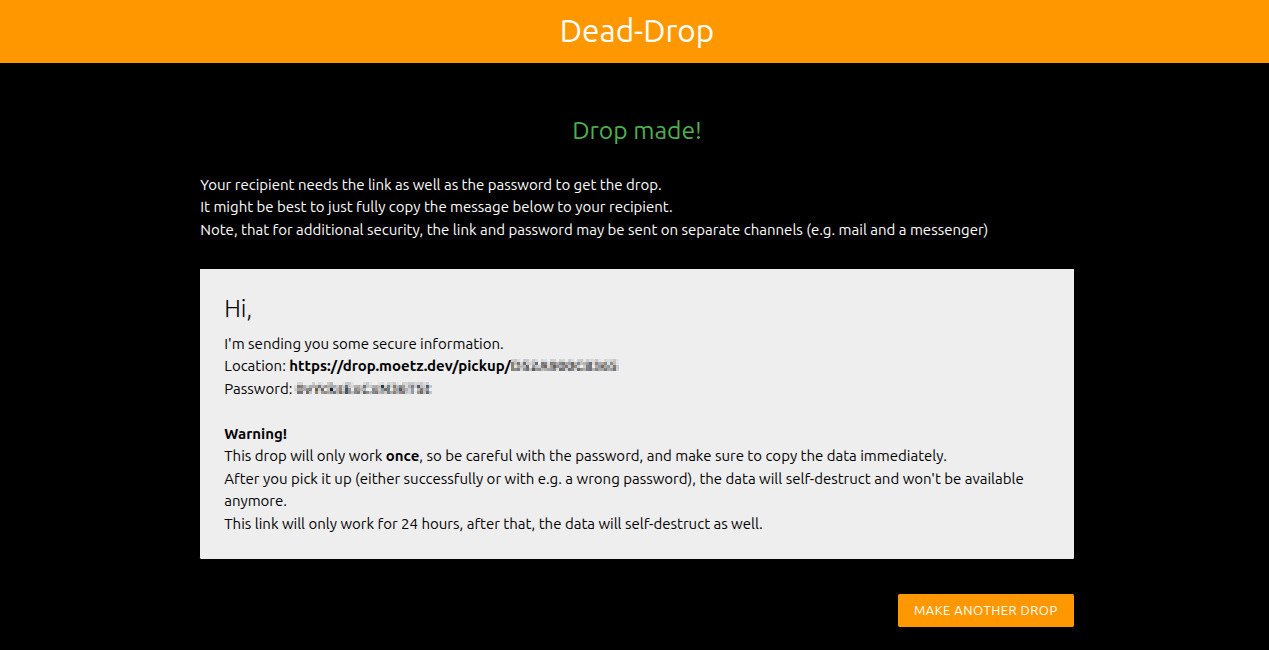
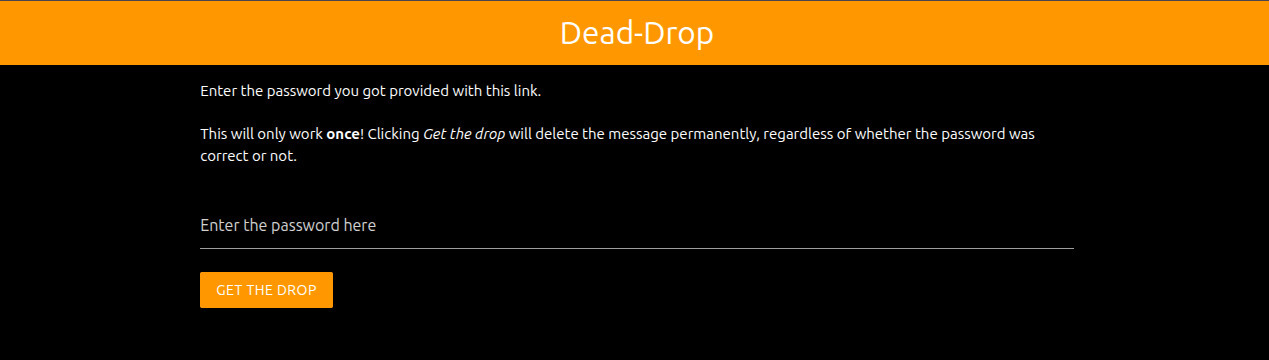
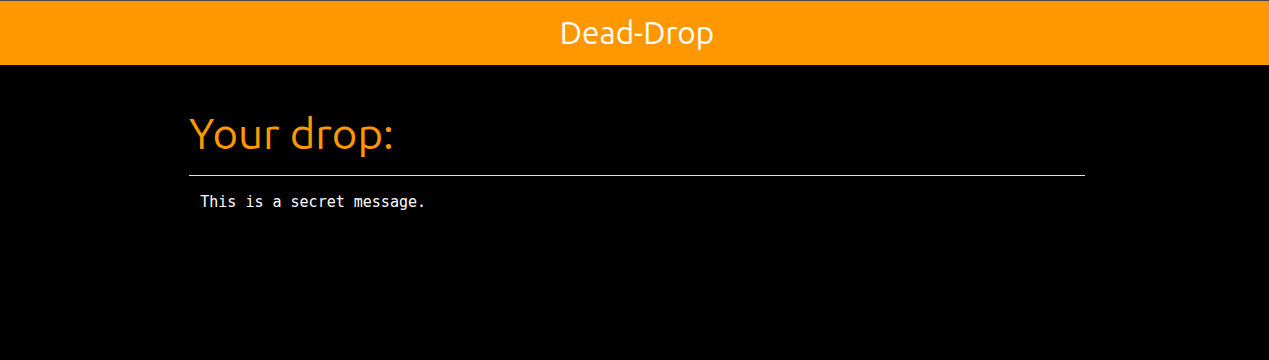
Basically, this service generates a random password in the browser, encrypts the message with sjcl in the browser itself, and then sends only the encrypted cipher to the server (which stores it for a maximum of 24 hours). So the server will never see the password that is required to encrypt the data. After that, the browser will show the link to pick up the drop as well as the generated password to the user. This text is then to be sent to the recipient of the message by any channel (e.g. email, chat or some other way of communication). The recipient will open the pickup-link, and will be prompted for the password. As soon as the password is entered, the encrypted cipher is fetched from the server (which will delete the data as soon as it's loaded once), and the browser will try to decrypt the ciphertext using the provided password. If that succeeds, the decrypted message will be presented. Otherwise, an error will be shown, and the message will be gone forever, as the encrypted ciphertext has already been cleaned from the server. Therefore, this dead-drop will truly only try to deliver the message once, and after that it's gone forever. Furthermore, if the link or ciphertext would have been intercepted by an attacker, the recipient would know as the drop is no longer available, signalling you to best not treat the sent information (e.g. password) as not secret anymore.
Feel free to try it out, use it to send passwords or other sensible information, or host it on your own!